In an era where digital communication is paramount, the need for secure transmission of information has never been more critical. Traditional cryptographic methods, while effective to a degree, are increasingly vulnerable to sophisticated attacks, particularly as computational power continues to grow. Enter quantum cryptography, a revolutionary approach that leverages the principles of quantum mechanics to create secure communication channels.
This innovative technology promises not only to enhance security but also to redefine the very foundations of how information is protected in the digital age. Quantum cryptography stands at the intersection of physics and information technology, offering a new paradigm for safeguarding sensitive data. By utilizing the unique properties of quantum bits, or qubits, it enables the creation of cryptographic keys that are theoretically immune to eavesdropping.
As the world becomes more interconnected and reliant on digital communication, understanding quantum cryptography’s principles and applications is essential for anyone interested in the future of secure communication.
Key Takeaways
- Quantum cryptography leverages principles of quantum mechanics to enable ultra-secure communication.
- It uses quantum properties like superposition and entanglement to detect eavesdropping.
- Offers significant security advantages over traditional cryptography, especially against quantum computer attacks.
- Faces challenges including technological complexity and implementation costs.
- Holds promising applications in national security and future-proofing data against quantum computing threats.
The Basics of Quantum Mechanics
To grasp the intricacies of quantum cryptography, one must first understand the fundamental concepts of quantum mechanics. At its core, quantum mechanics is a branch of physics that deals with the behavior of matter and energy at the smallest scales—typically at the level of atoms and subatomic particles. Unlike classical physics, which operates under deterministic laws, quantum mechanics introduces a level of unpredictability and complexity that challenges conventional understanding.
One of the most significant principles of quantum mechanics is superposition, which allows particles to exist in multiple states simultaneously until measured. This phenomenon is crucial for quantum computing and cryptography, as it enables qubits to represent both 0 and 1 at the same time. Another key concept is entanglement, where two particles become interconnected in such a way that the state of one instantly influences the state of the other, regardless of the distance separating them.
These principles form the backbone of quantum cryptography, providing a framework for secure communication that traditional methods cannot replicate.
The Principles of Quantum Cryptography
Quantum cryptography operates on several foundational principles derived from quantum mechanics. The most notable among these is the no-cloning theorem, which states that it is impossible to create an identical copy of an arbitrary unknown quantum state. This principle ensures that any attempt to intercept or duplicate a quantum key will inevitably alter its state, alerting the communicating parties to potential eavesdropping.
Another essential principle is the use of quantum key distribution (QKD), which allows two parties to generate a shared secret key with security guaranteed by the laws of quantum physics. QKD protocols, such as BB84 and E91, utilize the properties of qubits to ensure that any interception or measurement by an unauthorized party will introduce detectable anomalies in the key exchange process. This inherent security feature distinguishes quantum cryptography from traditional methods, which rely on mathematical complexity rather than physical laws.
How Quantum Cryptography Works
The operation of quantum cryptography can be illustrated through a simplified explanation of quantum key distribution. In a typical QKD scenario, two parties—commonly referred to as Alice and Bob—wish to establish a secure communication channel. They begin by sending qubits encoded with information about their shared secret key over a quantum channel.
These qubits can be represented using various physical systems, such as photons or atoms. As Alice transmits her qubits to Bob, they both measure their received states independently. Due to the principles of quantum mechanics, any attempt by an eavesdropper—often referred to as Eve—to intercept or measure these qubits will disturb their states.
After the transmission, Alice and Bob compare a subset of their measurements over a classical channel to detect any discrepancies that may indicate eavesdropping. If no anomalies are found, they can proceed to use the remaining measurements to generate a secure shared key.
Advantages of Quantum Cryptography over Traditional Cryptography
| Metric | Description | Typical Value / Range | Unit |
|---|---|---|---|
| Quantum Bit Error Rate (QBER) | Percentage of bits received incorrectly due to noise or eavesdropping | 1% – 5% | % |
| Key Generation Rate | Rate at which secure cryptographic keys are generated | 1,000 – 1,000,000 | bits per second (bps) |
| Communication Distance | Maximum distance over which secure quantum communication is maintained | 10 – 400 | kilometers (km) |
| Photon Source Efficiency | Probability of generating a single photon per pulse | 10% – 80% | % |
| Detector Efficiency | Probability that a photon is successfully detected | 50% – 90% | % |
| Secure Key Rate | Rate of final secure key bits after error correction and privacy amplification | 100 – 500,000 | bits per second (bps) |
| Latency | Time delay in key distribution and communication | Milliseconds to seconds | ms / s |
| Quantum Channel Loss | Signal attenuation in the quantum channel | 0.2 – 0.35 | dB/km |
One of the most significant advantages of quantum cryptography is its unparalleled security. Unlike traditional cryptographic methods that rely on complex mathematical algorithms, which can be broken with sufficient computational power or advanced techniques, quantum cryptography’s security is rooted in the fundamental laws of physics. This means that even with future advancements in computing technology, such as quantum computers capable of breaking classical encryption schemes, quantum cryptography remains secure against such threats.
The moment an unauthorized party tries to intercept or measure the qubits being transmitted, their presence is immediately revealed through observable changes in the key exchange process. This proactive approach to security allows Alice and Bob to take necessary precautions before proceeding with their communication, ensuring that sensitive information remains confidential.
Challenges and Limitations of Quantum Cryptography
Despite its promising advantages, quantum cryptography is not without its challenges and limitations. One significant hurdle is the current technological constraints associated with implementing QKD systems over long distances. Quantum signals tend to degrade over distance due to factors such as scattering and absorption in optical fibers or atmospheric interference when transmitted through free space.
As a result, practical implementations are often limited to relatively short distances unless advanced techniques like quantum repeaters are employed. Moreover, while quantum cryptography provides robust security against eavesdropping, it does not inherently protect against all forms of cyber threats. For instance, if Alice and Bob’s devices are compromised or if they fall victim to social engineering attacks, their communication could still be at risk.
Therefore, integrating quantum cryptography into existing security frameworks requires careful consideration and additional layers of protection.
Current Applications of Quantum Cryptography
As research and development in quantum cryptography continue to advance, several applications have emerged across various sectors. One notable area is secure communications for government agencies and military organizations that require high levels of confidentiality for sensitive information. Countries like China have already begun deploying QKD networks for secure communication between government officials and military personnel.
In addition to governmental applications, financial institutions are exploring quantum cryptography for securing transactions and protecting customer data from potential breaches. The banking sector’s reliance on secure communication makes it an ideal candidate for adopting this cutting-edge technology. Furthermore, industries such as healthcare and telecommunications are also investigating how quantum cryptography can enhance data protection and privacy in their operations.
Future Potential of Quantum Cryptography
The future potential of quantum cryptography is vast and multifaceted. As technology continues to evolve, researchers are working on overcoming current limitations related to distance and scalability. Innovations such as satellite-based QKD systems could enable global secure communication networks that transcend geographical barriers.
This would revolutionize how sensitive information is transmitted across borders and enhance international cooperation in cybersecurity efforts. Moreover, as more organizations recognize the importance of data security in an increasingly digital world, the demand for quantum cryptographic solutions is likely to grow. This could lead to further investment in research and development, resulting in more efficient protocols and practical implementations that can be integrated into existing infrastructures seamlessly.
Quantum Cryptography in the Age of Quantum Computing
The advent of quantum computing presents both challenges and opportunities for quantum cryptography. On one hand, powerful quantum computers could potentially break traditional encryption methods that rely on mathematical complexity. However, this same technology also provides a unique opportunity for enhancing quantum cryptographic systems.
Researchers are exploring how advancements in quantum computing can improve QKD protocols and increase their efficiency.
As both fields continue to develop in tandem, they may ultimately complement each other in creating a more secure digital landscape.
Quantum Cryptography and National Security
National security agencies around the world are increasingly recognizing the strategic importance of quantum cryptography in safeguarding sensitive communications against espionage and cyber threats. As nations invest in developing their own QKD systems, there is a growing emphasis on establishing secure communication channels that can withstand potential attacks from adversaries equipped with advanced technologies. The integration of quantum cryptography into national security frameworks not only enhances communication security but also fosters international collaboration on cybersecurity initiatives.
By sharing knowledge and resources related to quantum technologies, countries can work together to create a more resilient global infrastructure against emerging threats.
The Future of Secure Communication with Quantum Cryptography
As society becomes more reliant on digital communication, the need for robust security measures will only intensify. Quantum cryptography represents a groundbreaking advancement in this field, offering unparalleled security based on the principles of quantum mechanics. While challenges remain in terms of implementation and scalability, ongoing research and development hold great promise for overcoming these obstacles.
The future of secure communication lies in harnessing the power of quantum technologies to create resilient systems capable of protecting sensitive information against evolving threats. As organizations across various sectors begin to adopt quantum cryptographic solutions, they will pave the way for a new era of secure communication that transcends traditional boundaries and safeguards privacy in an increasingly interconnected world.
Quantum cryptography is revolutionizing secure communication by leveraging the principles of quantum mechanics to ensure that information remains confidential and tamper-proof. For a deeper understanding of this cutting-edge technology and its implications for the future of secure communication, you can read more in this related article on quantum cryptography at My Cosmic Ventures.
WATCH THIS! Quantum Physics Just PROVED We’re Living in a Simulation!
FAQs
What is quantum cryptography?
Quantum cryptography is a method of secure communication that uses the principles of quantum mechanics to encrypt and transmit data, ensuring that any attempt at eavesdropping can be detected.
How does quantum cryptography ensure secure communication?
Quantum cryptography relies on the properties of quantum particles, such as photons, which cannot be measured or copied without altering their state. This allows the detection of any interception during the transmission of encryption keys, making communication highly secure.
What is Quantum Key Distribution (QKD)?
Quantum Key Distribution is a technique used in quantum cryptography to securely share encryption keys between parties. It uses quantum states to transmit keys, ensuring that any eavesdropping attempt is immediately noticed.
Is quantum cryptography completely unbreakable?
While quantum cryptography offers a very high level of security based on the laws of physics, practical implementations may have vulnerabilities due to hardware imperfections or side-channel attacks. However, it is currently considered more secure than classical cryptographic methods.
What are the main applications of quantum cryptography?
Quantum cryptography is primarily used for secure communication in government, military, financial institutions, and other sectors requiring high levels of data security. It is also being explored for securing future internet infrastructure.
Can quantum cryptography be used over long distances?
Quantum cryptography faces challenges over long distances due to photon loss and signal degradation. However, advancements such as quantum repeaters and satellite-based QKD are being developed to extend its range.
How does quantum cryptography differ from classical cryptography?
Classical cryptography relies on mathematical algorithms and computational difficulty for security, whereas quantum cryptography uses the fundamental principles of quantum mechanics, making it theoretically immune to computational attacks.
Is quantum cryptography widely available today?
Quantum cryptography is still in the early stages of commercial deployment. Some companies and research institutions offer quantum cryptographic solutions, but widespread adoption is limited by technical and cost challenges.
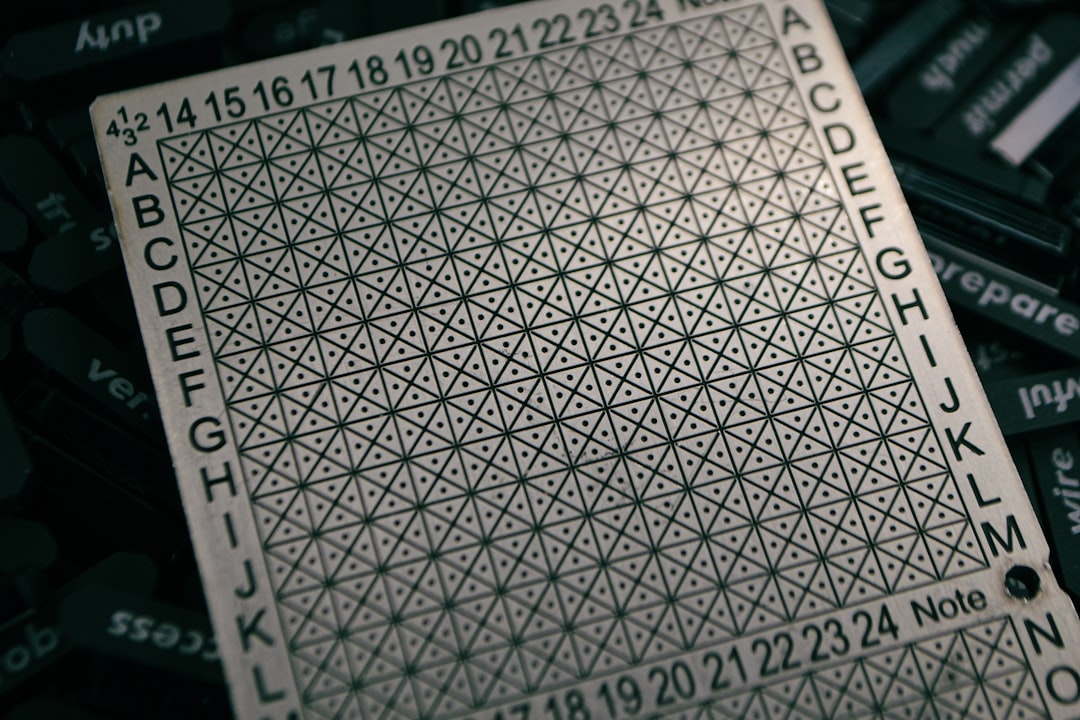
What equipment is needed for quantum cryptography?
Quantum cryptography requires specialized hardware such as single-photon sources, detectors, and quantum random number generators, along with classical communication channels for key reconciliation and error correction.
Will quantum computers break current cryptographic systems?
Quantum computers have the potential to break many classical cryptographic algorithms by efficiently solving problems like integer factorization. Quantum cryptography provides a way to secure communication against such future threats.